Axios Supply Chain Attack Hits npm as Claude Code Source Leaks via Source Maps
A critical supply chain attack on axios dominated the conversation today, with the npm package's 100M+ weekly downloads potentially compromised by injected malware. Meanwhile, Anthropic accidentally published Claude Code's full source via a .map file in their npm registry, and Google Research revealed a 20x improvement to Shor's algorithm that could break ECDSA encryption by 2029.
Daily Wrap-Up
Today was one of those days where the security stories wrote themselves. The axios supply chain attack sent shockwaves through the JavaScript ecosystem, and the timing couldn't have been more ironic: just as developers were scrambling to audit their lockfiles, Anthropic's own Claude Code source got exposed through a forgotten source map in their npm package. The juxtaposition of a sophisticated supply chain compromise alongside a basic build configuration oversight tells you everything about the current state of software security. We're simultaneously facing nation-state-level threats and tripping over our own shoelaces.
On the product side, the walls between AI coding tools continue to dissolve. OpenAI officially blessed a plugin letting you call Codex from Claude Code, which feels like a watershed moment for interoperability. Anthropic shipped computer use in Claude Code, Qwen dropped their 3.5-Omni model with "Audio-Visual Vibe Coding," and the overall vibe is that the coding agent space is converging fast. The most entertaining moment was easily @TukiFromKL's takedown of Anthropic's source leak: "it's like locking every door in your house, installing cameras, hiring armed guards, then accidentally uploading your floor plans to Google Maps."
Underneath all the chaos, Google quietly dropped what might be the most consequential news of the week: a 20x efficiency improvement to Shor's algorithm that puts practical quantum cryptography attacks within reach by 2029. They were so spooked by their own results that they published a zero-knowledge proof instead of the actual circuits. The most practical takeaway for developers: add min-release-age=7 to your .npmrc right now, pin your dependency versions, and start treating every npm install as a potential attack surface. The axios incident won't be the last.
Quick Hits
- @adcock_brett sat down with Shawn Ryan for a 3-hour interview covering humanoid robots, flying cars, and next-gen AI interfaces.
- @EntireHQ shipped OpenAI Codex integration, Amazon's Kiro agent, and Windows support in their latest dispatch.
- @theo called out JavaScript bloat as "slowly destroying the web" and shared a breakdown of how to fight it.
- @DeRonin_ posted a detailed 7-stage playbook for growing an app from 0 to 100K users, emphasizing the manual "ugly stage" most founders skip.
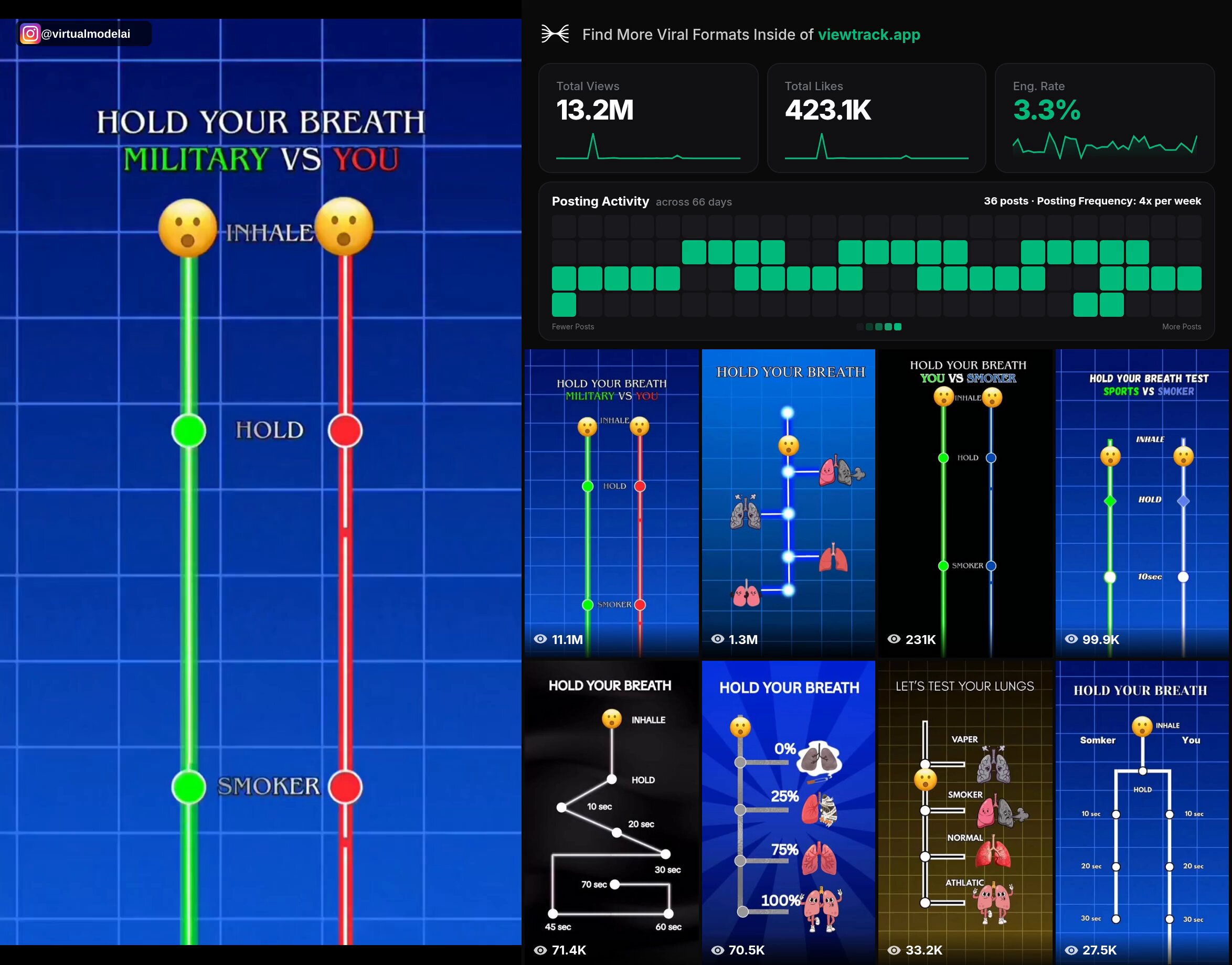
- @ErnestoSOFTWARE highlighted apps making $80K/month using breath-holding challenge videos as a viral hook for breathing apps.
- @TheAhmadOsman teased a GPU giveaway with "multiples" of GPUs and potentially full machines.
- @ashebytes interviewed @timourxyz about Edge City's pop-up villages for frontier tech builders.
- @tejessrivalsan announced EGO-BIRD, 100,000 hours of POV bird footage for training autonomous drones.
- @itsolelehmann shared a Claude Code skill implementing Karpathy's "LLM Council" method for getting more trustworthy AI advice through adversarial multi-model debate.
- @Starlink promoted 400+ Mbps speeds for streaming and remote work.
- @steipete RT'd a prediction that 2026 will be the year everyone discovers how limited "long context" really is.
- @lateinteraction RT'd research on autonomously improving LLM harnesses on active problems.
- @RayFernando1337 RT'd @alvinsng on combining agentic code review with agentic QA.
- @Scobleizer flagged a must-read on competitive moats for entrepreneurs.
The Axios Supply Chain Attack
The biggest security story of the day landed when @feross broke the news that axios 1.14.1, one of npm's most depended-upon packages with 100M+ weekly downloads, had been compromised. The latest version quietly pulled in plain-crypto-js@4.2.1, a package that didn't exist before today, containing obfuscated malware that executes shell commands, stages payloads in temp directories, and destroys forensic evidence after execution. This is textbook supply chain installer malware hitting at massive scale.
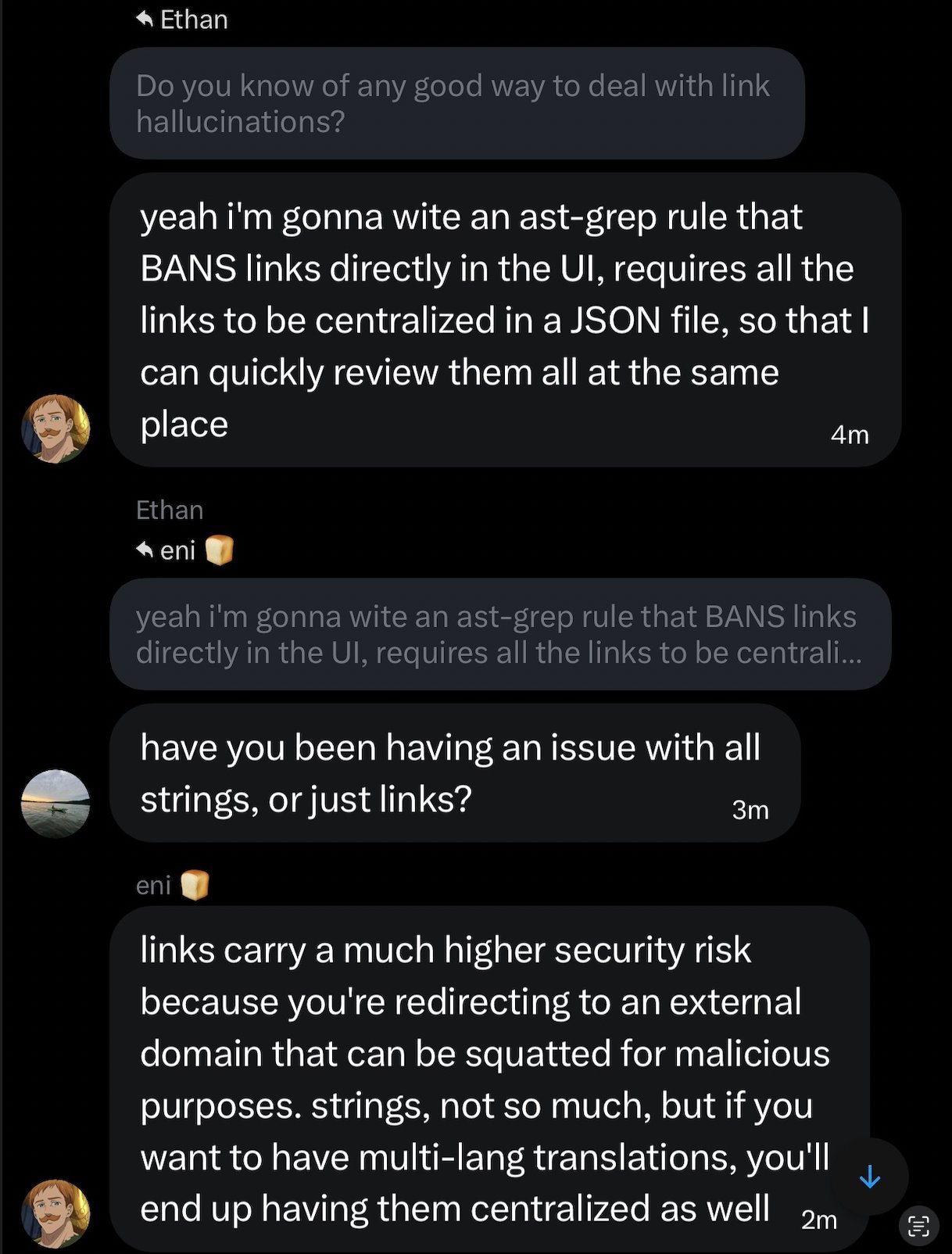
The community response was swift but anxious. @neural_avb captured the mood: "Axios is literally everywhere. If your project does a http request, its probably using axios under the hood. I feel there are more poisoned packages out there that nobody has discovered yet." @affaanmustafa connected it to broader agentic security concerns, noting that "skills and rules that point at external docs are supply chain liabilities. If a link can change without your approval, it can become an injection source later."
The practical advice converged quickly. @feross recommended setting min-release-age=7 in .npmrc and installing Socket for GitHub. @airesearch12 shared the equivalent Python protection via uv.toml. @swyx highlighted an interesting angle: Devin Review caught the attack for Cognition customers before it was publicly announced, making the case that "there is basically 0 reason not to have a Review bot enabled for all the things." The argument that AI coding agents are now better security reviewers than humans is provocative, but when a generalist agent catches a supply chain attack 45 minutes after injection, it's hard to argue with the results.
Claude Code Source Leak
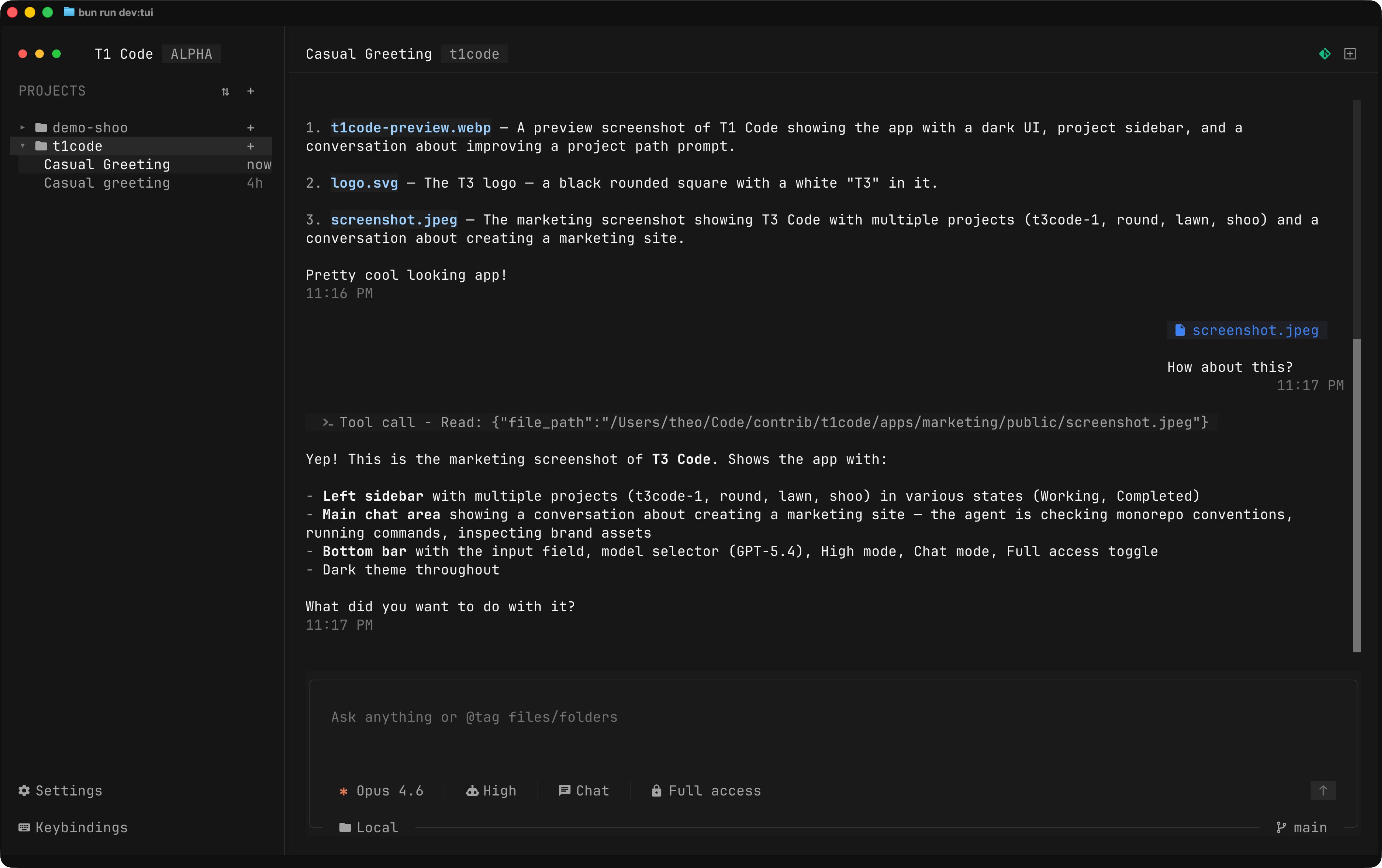
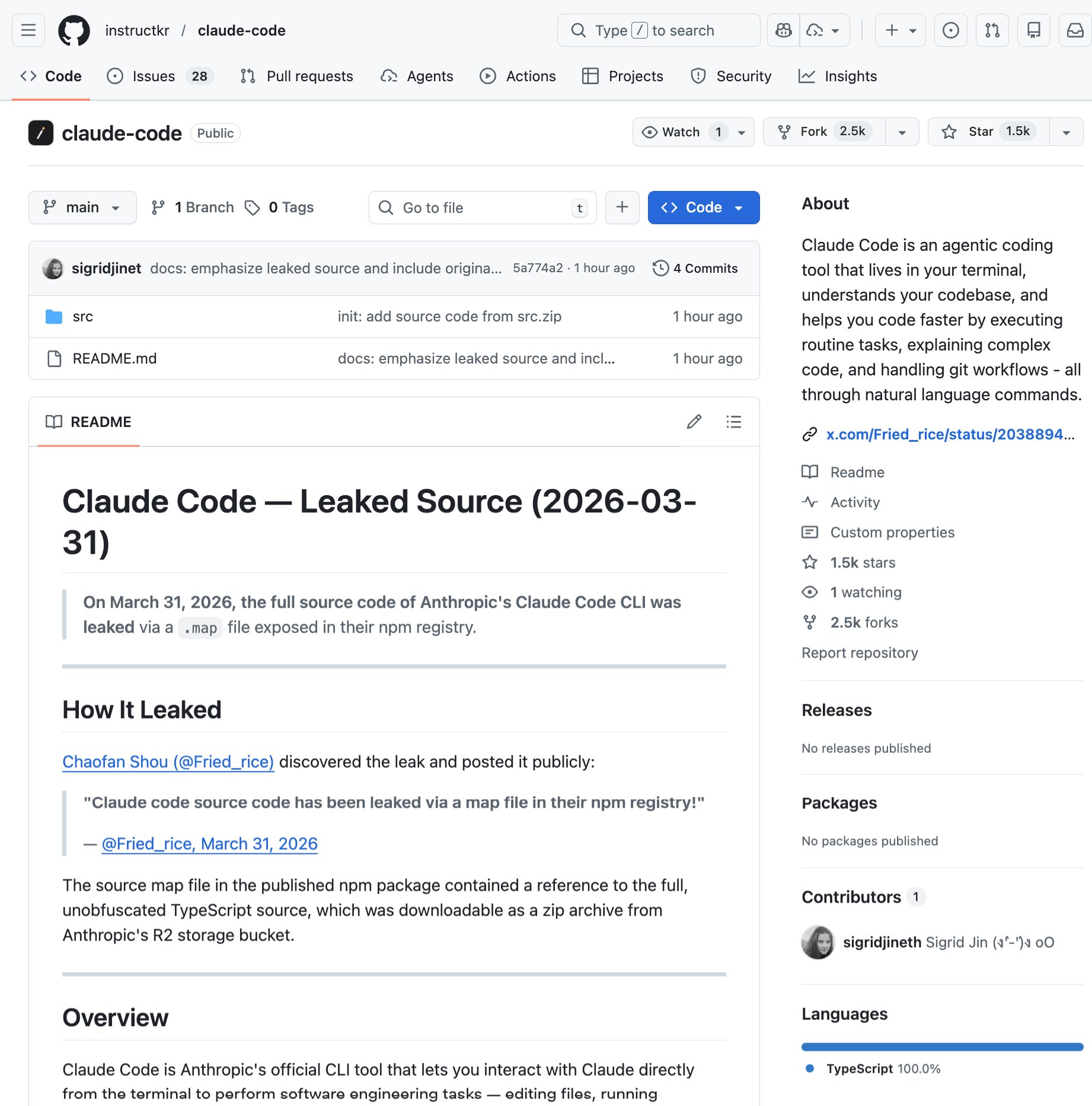
In a twist that practically writes its own punchline, Anthropic accidentally published Claude Code's full source code via a .map file included in their npm package. Source maps are build artifacts that reverse minified code back to its original form, and someone on the team apparently shipped one straight to the registry. Within an hour, @Fried_rice had flagged it, and @realsigridjin had backed it up on GitHub where it quickly gained 1,500+ stars.
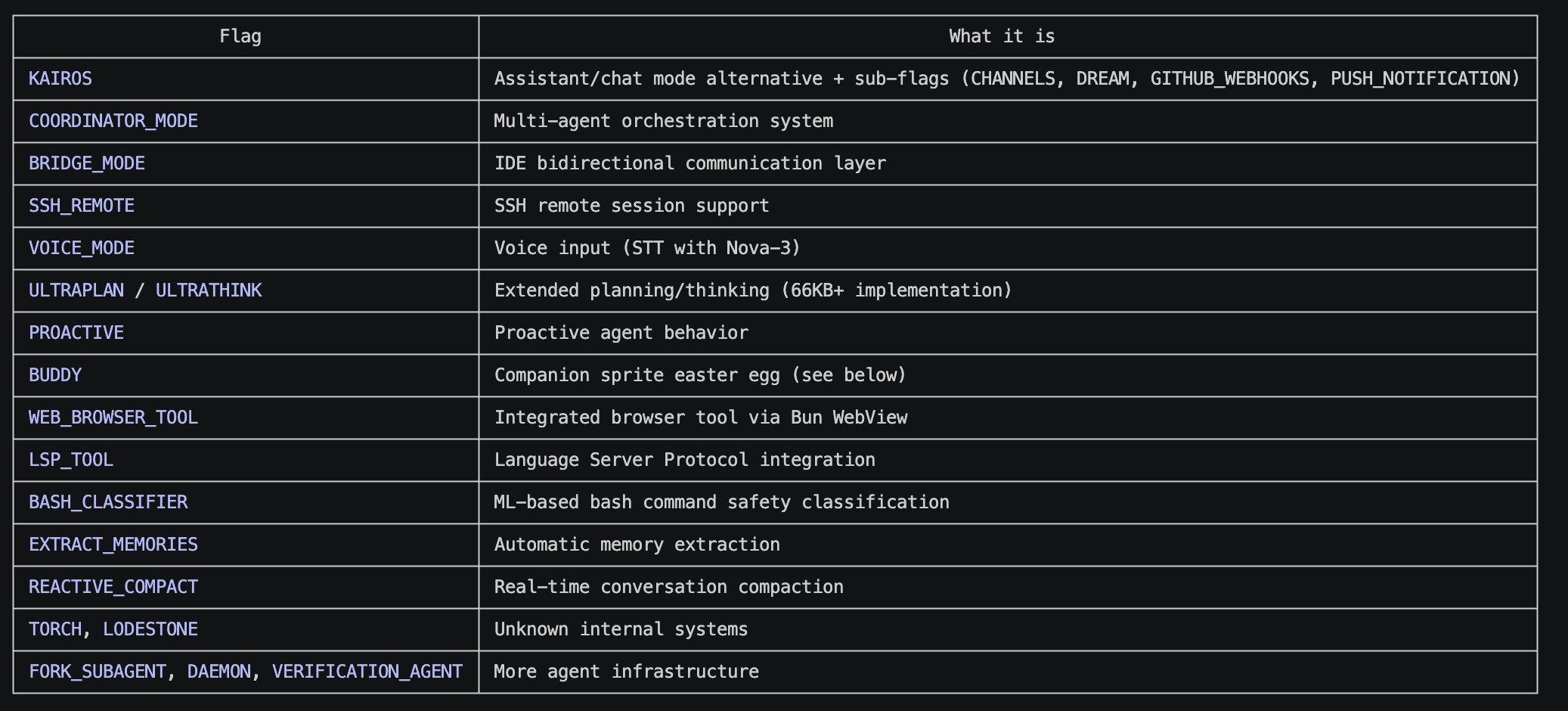
@TukiFromKL delivered the most memorable commentary: "this is the same company that told Congress AI is an existential threat... and they got exposed by a config file that any mid-level engineer would've caught in a code review." @himanshustwts dug into the technical details, reporting that Claude Code is "built with React + Ink (terminal UI) on Bun runtime, ~512k lines of TypeScript" with "major gated features that aren't public yet."
Rather than just dunking on the mistake, @vineetwts turned lemons into lemonade by creating documentation over the leaked codebase explaining its pipeline, context handling, and memory system. The incident is a reminder that operational security failures don't require sophisticated attacks. Sometimes the most sensitive code walks out the front door because someone forgot to add *.map to their .npmignore. Multiple people RT'd the news including @flaviocopes and @Hesamation, suggesting the developer community found this both alarming and deeply relatable.
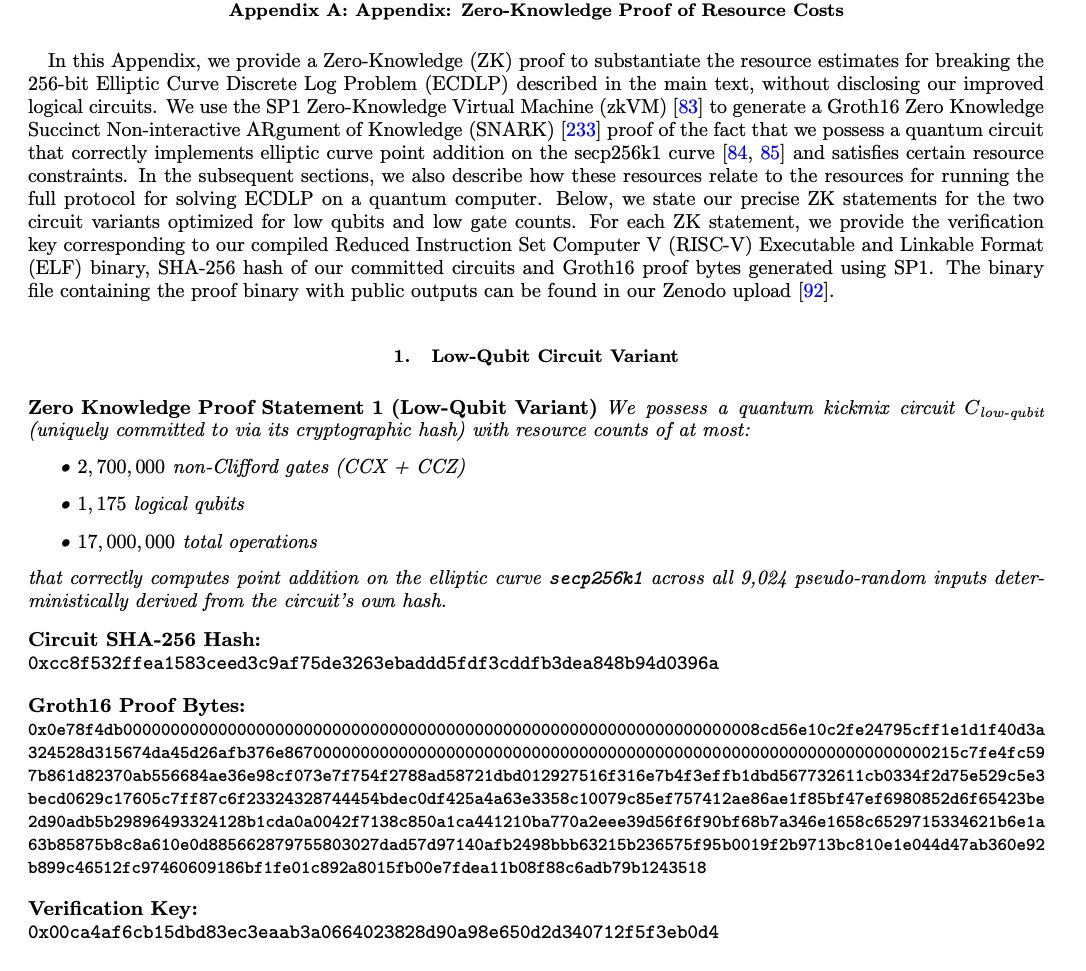
Google's Quantum Cryptography Breakthrough
Quietly overshadowed by the supply chain drama, Google Research revealed what may be the most consequential security development of the year. @hosseeb summarized the findings: Google demonstrated "a ~20x more efficient implementation of Shor's algorithm that could break ECDSA keys within minutes with ~500K physical qubits." The timeline for practical quantum attacks on current encryption has shifted from the mid-2030s to potentially 2029.
What makes this extraordinary is Google's response to their own discovery. As @hosseeb noted, "they believe this result is so severe that they are not publishing the actual circuits. They instead published a ZKP proving that they know of the quantum circuit with these properties." Publishing a zero-knowledge proof of a cryptographic attack instead of the attack itself is unprecedented in the research community. @mreiffy paraphrased Google's position bluntly: "We can now break it. We can prove it. We're just not going to tell you how." For blockchain projects in particular, @hosseeb's conclusion is stark: "All blockchains need a transition plan ASAP. Post-quantum is no longer a drill."
AI Coding Tools: The Great Convergence
The interoperability story of the day was the Codex plugin for Claude Code, officially endorsed by both sides. @romainhuet from OpenAI framed it as ecosystem-building: "We've seen Claude Code users bring in Codex for code review and use GPT-5.4 for more complex tasks, so we thought: why not make that easier?" @reach_vb shared the practical commands: /codex:review for standard review, /codex:adversarial-review for challenge review, and /codex:rescue to let Codex fix your code. @OpenAIDevs RT'd the announcement, making the cross-company endorsement explicit.
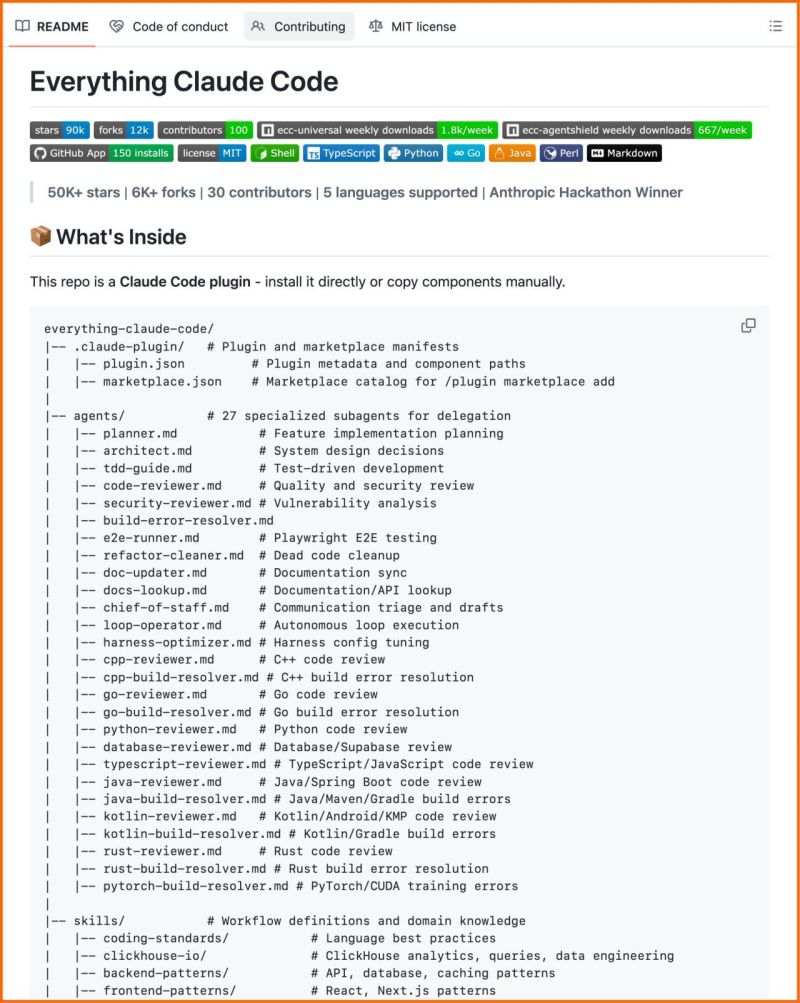
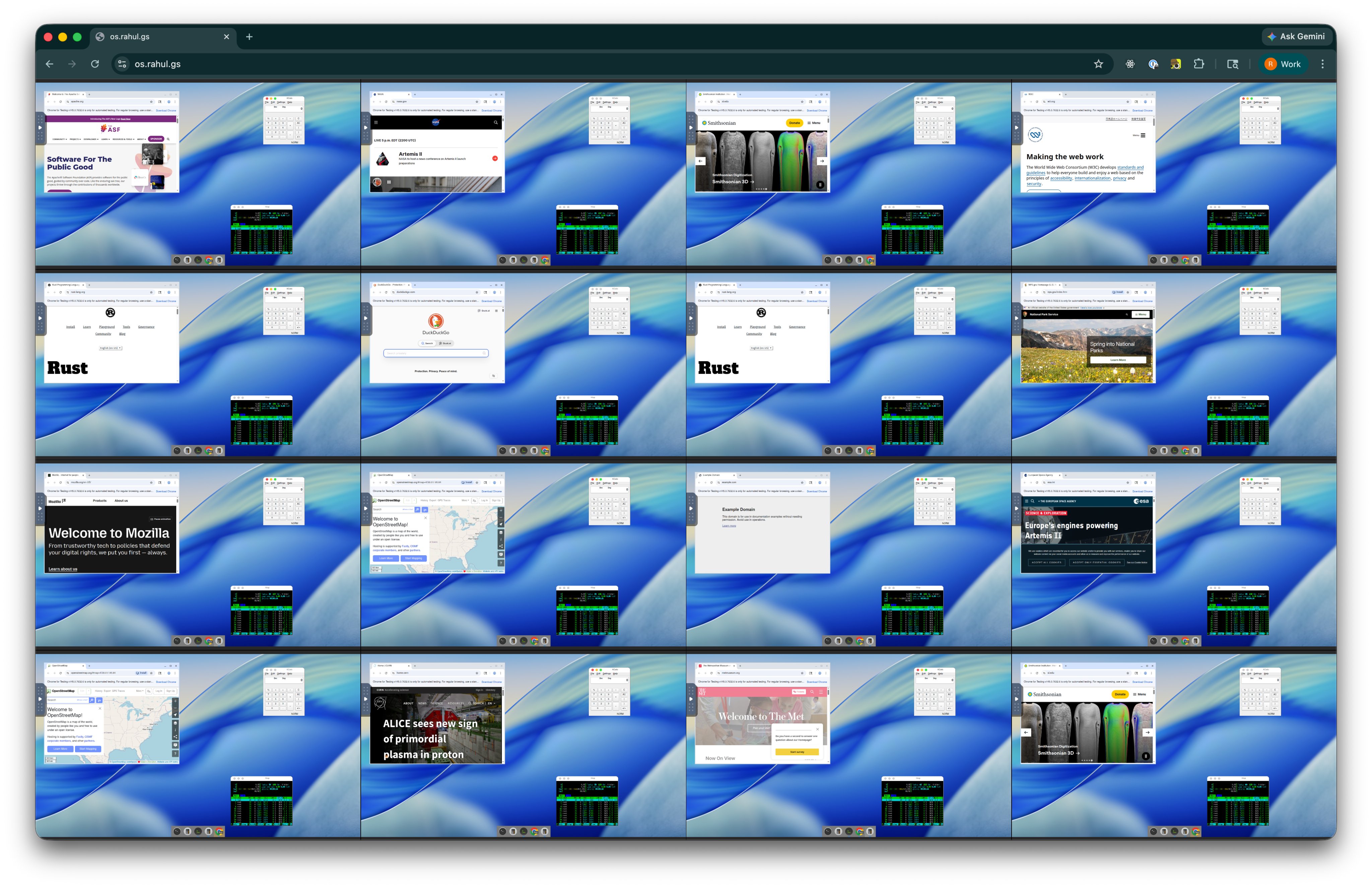
Meanwhile, @felixrieseberg announced that computer use is now available in Claude Code, letting Claude control your mouse and keyboard from the CLI with per-app permissions. @rahulgs showed off something even more ambitious: hundreds of VMs running in a browser, each controlled by an agent, with humans able to step in CCTV-style when agents get stuck. And @dr_cintas highlighted an Anthropic hackathon winner who open-sourced a massive Claude Code setup with 27 agents, 64 skills, and 33 commands, claiming 60% documented cost reduction.
Codex Security Vulnerability
On the security front for coding agents specifically, @kmcquade3 disclosed a critical vulnerability in OpenAI Codex that allowed exfiltration of GitHub tokens to an attacker's C2 server. The attack vector was command injection via GitHub branch names in task creation requests, granting "lateral movement and R/W access to a victim's entire code base." This discovery by @crew7sec at @btphantomlabs underscores that as coding agents gain more permissions and access, their attack surface grows proportionally. The irony of discovering a Codex vulnerability on the same day Codex ships a Claude Code integration is not lost on anyone paying attention.
Qwen 3.5-Omni and Local AI
Alibaba's Qwen team launched Qwen3.5-Omni, a native omni-modal model handling text, image, audio, and video with real-time interaction. The standout feature is "Audio-Visual Vibe Coding," where you describe your vision to a camera and the model builds a functional website or game. It handles up to 10 hours of audio or 400 seconds of 720p video natively, recognizes 113 languages, and speaks 36. @MatthewBerman acknowledged "Qwen cooked" while questioning sustainability.
On the local inference side, @somewheresy reported running a Q8 quantized Qwen3.5-27B (fine-tuned on Claude Opus 4.6 reasoning data via Unsloth) on a 64GB Mac Mini M4, calling it "pretty baller." The model has been trending #1 on Hugging Face for three weeks. Meanwhile, @techNmak flagged Microsoft's VibeVoice, a 0.5B parameter model doing real-time TTS at 300ms latency, quietly sitting on GitHub. The local AI ecosystem continues to mature at a pace that makes last year's capabilities look quaint.
Claude Code Tips and Workflows
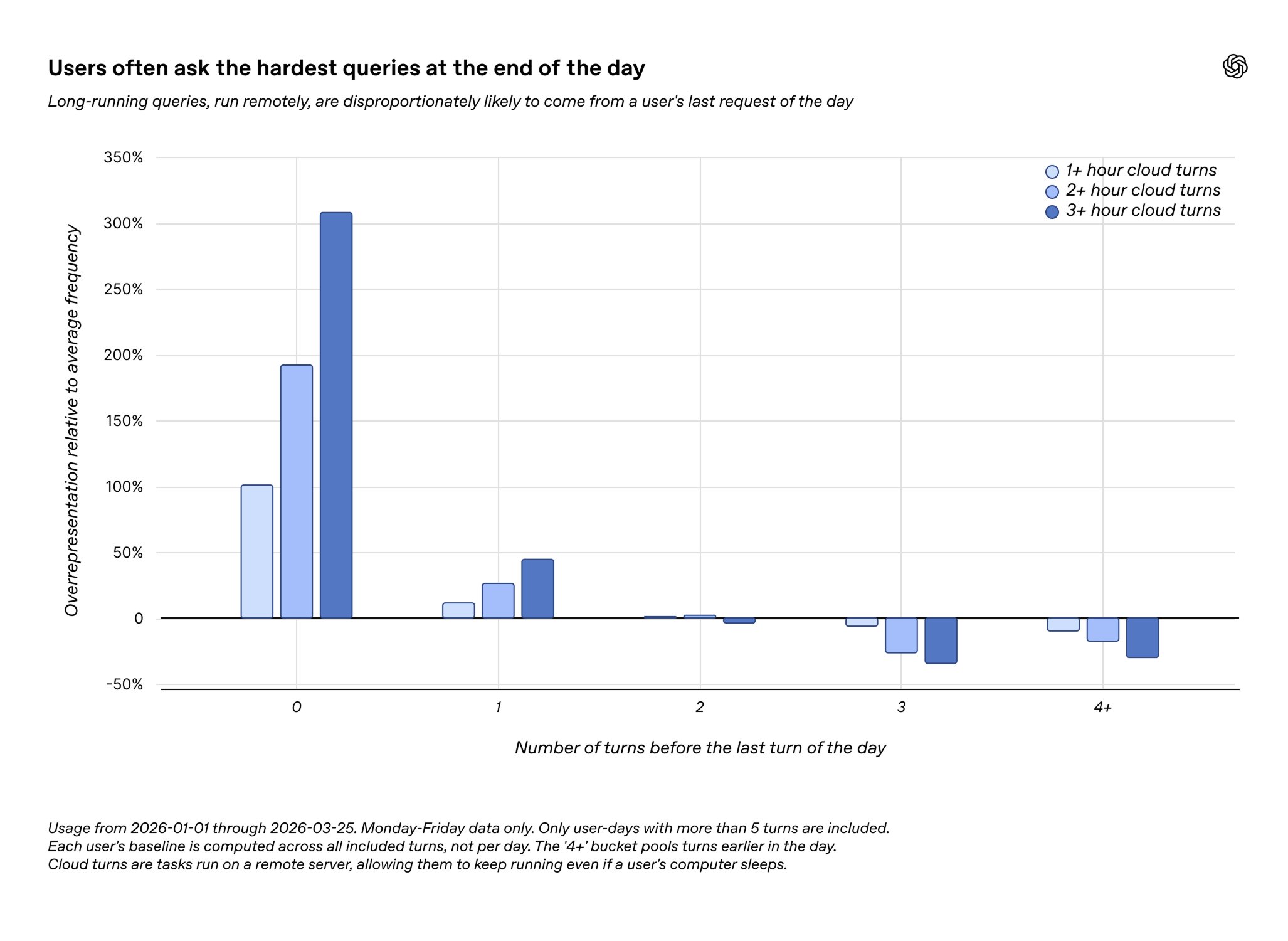
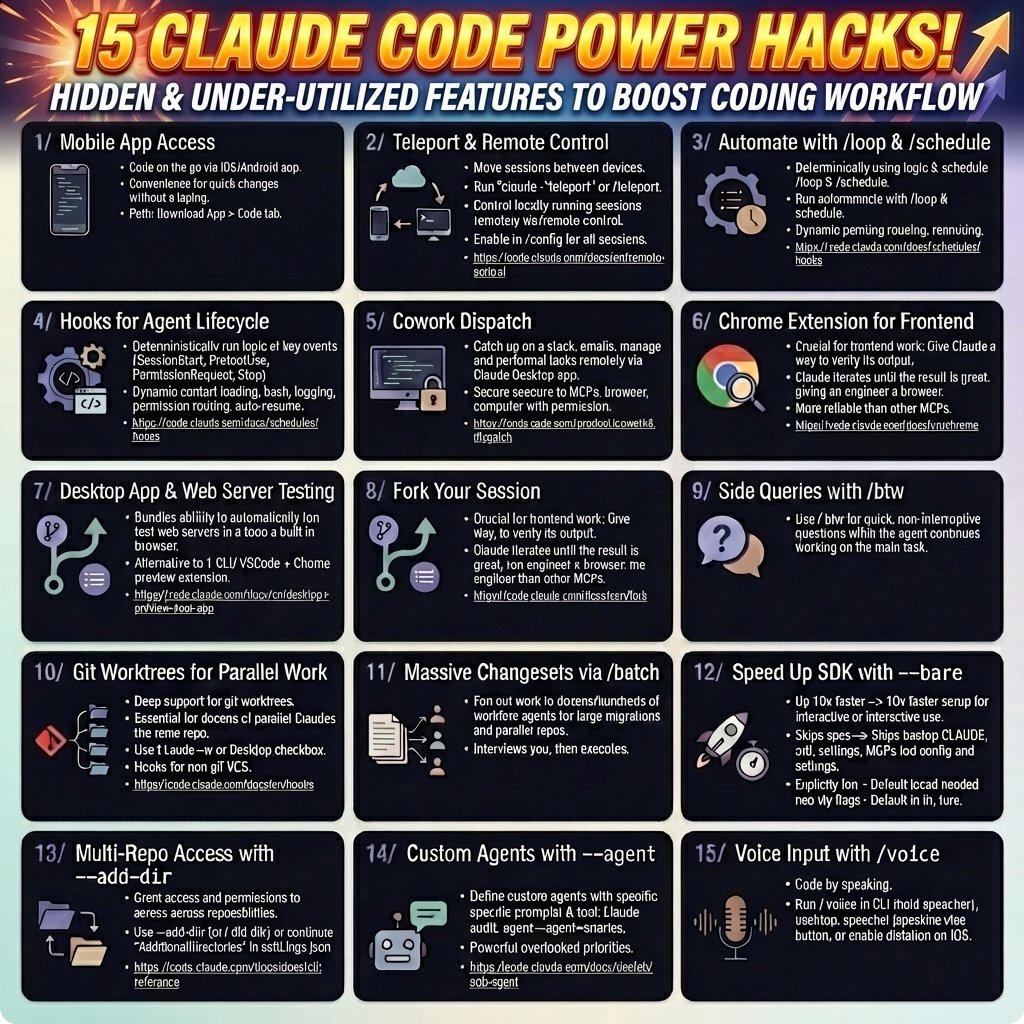
Beyond the source leak drama, Claude Code had a productive day on the tips front. @minchoi highlighted @bcherny's thread on hidden and under-utilized Claude Code features that "literally boost your coding workflow." @sopersone posted a humorous video about "Claude coders right now" alongside Python coders and Polymarket traders. And @OpenAIDevs shared data showing developers are delegating long-running tasks like refactors and architecture planning to Codex at the end of the day, essentially "getting work done while they sleep." The pattern is clear: coding agents are becoming the night shift that developers never had.
Sources
How to grow your app from 0 to 100k users (PLAYBOOK): by the end, you'll know how to: - get your first 10 paying customers without a funnel - build organic growth that compounds monthly - know exactly when to spend money and when not to - turn your users into your best acquisition channel here's the full 7-stage roadmap: Stage 1 (0-10): find your niche and sell one person at a time the biggest mistake is building for "everyone" you don't need a market. you need 10 people who feel the pain so badly they'd pay you today how to find them: > pick one specific audience (who can potentially buy the solution) > go where they already complain: X, Reddit, Slack communities, Discord servers > read their exact words. the language they use to describe the pain = your marketing copy > DM 50 people. not pitching. just asking "what's the most frustrating part of [problem]?" your first 10 customers should feel like you read their mind with my own product, I went to a conference and just talked about the problem I was solving 5 people wanted to buy before I had anything to sell, 50 are ready to test (at 2x price from basic costs) metric to watch: conversion from conversation to "shut up and take my money" mistake to avoid: building features before talking to humans -------- Stage 2 (10-100): do things that don't scale forget funnels. forget ads. forget automation this stage is manual and it's supposed to be how to get to 100: > send 20-30 personalized DMs daily on X, Reddit, LinkedIn (not cold outreach!) > post daily in communities where your audience already lives > jump in free onboarding calls, watch how people use your product > when someone leaves, always ask why (it happens often lol) what this gives you: 1: real feedback that shapes your product into something people actually need 2: language and objections you'll use in marketing for the next 2 years 3: early advocates who tell their friends the first 100 users will teach you more than any analytics dashboard ever will don't scale until you've fixed everything these 100 people found broken metric to watch: how many users come back after week 1 mistake to avoid: automating too early and losing the human feedback loop -------- Stage 3 (100-500): fix retention before chasing growth this is where most apps die silently they keep acquiring users while losing them out the back door before you spend a single minute on growth, answer these: 1: what % of users are still active after 7 days? 30 days? 2: where exactly do people drop off in onboarding? 3: what does your "WOW moment" look like and how fast do users reach it? how to fix retention: > cut time to value. 10 steps to feel the product? make it 3 > one email sequence that gets users to their first win in 24hrs > remove features that confuse more than they help > talk to churned users. after 10 calls the pattern is obvious your target: get churn below 5% monthly before moving to stage 4 because growing with 15% churn is like filling a bucket with a hole in it metric to watch: monthly churn rate and day-1 retention mistake to avoid: adding features instead of fixing the experience -------- Stage 4 (500-1k): build your organic engine and referral system now you've got the right to scale two engines to build simultaneously: content engine: - pick 2 platforms max (X + LinkedIn, or YouTube + TikTok depending on your audience) - post 5x/week minimum. document your building process, share insights, show results - every post should teach one thing or prove one result - repurpose: one idea = 1 long post + 3 short posts + 1 thread across platforms referral engine: - trigger "invite a friend" right when users feel the most value - reward both sides: extended trial, premium feature, or credit - make sharing one click with a pre-written message - track top referrers and treat them like VIPs this is where growth starts compounding. content brings strangers. referrals bring warm leads. both are free metric to watch: viral coefficient (how many new users each existing user brings) mistake to avoid: spreading across 5 platforms and doing all of them poorly -------- Stage 5 (1k-10k): partnerships, affiliates, and first paid experiments organic alone hits a ceiling. now you layer partnerships: > find products with the same audience but no competition > propose co-marketing: joint webinars, shared newsletters, bundles > one right partnership can bring 500+ users overnight affiliates and BDs: > launch an affiliate program with 20-30% recurring commission > recruit creators who already talk to your audience > find 2-3 BDs to sell your product on commission base first paid channels: > only test ads when you know your CAC and LTV cold > start with retargeting (cheapest and highest intent) > test one cold channel: Meta for B2C, LinkedIn/Google for B2B > $500-1k/mo to test. scale only what's profitable in 30 days metric to watch: CAC to LTV ratio (aim for 1:3 minimum) mistake to avoid: spending on ads before your funnel converts organically -------- Stage 6 (10k-50k): scale what works, kill what doesn't at this stage you already know your channels. now it's about efficiency what to do: 1: double down on your top 2 channels. kill the rest 2: make your first growth hire 3: automate onboarding, emails, and referral tracking 4: build a community around the product: Discord, Slack, or Circle the community is your moat: > users help each other (reduces support costs) > feature requests come directly from power users > community members have 2-3x higher retention than non-members > it creates switching costs that competitors can't copy metric to watch: revenue per employee and growth rate month over month mistake to avoid: hiring too fast and burning cash before the model is proven -------- Stage 7 (50k-100k): brand, moat, and paid scale you're no longer just an app. you're a brand how to think about this stage: > brand is why someone picks you over 10 alternatives without comparing features > invest in design, storytelling, positioning, make the product feel inevitable > go bigger: conferences, podcasts, media, Product Hunt at scale paid acquisition at scale: - increase ad budget on proven channels - test new channels (influencer marketing, sponsorships, programmatic) - build lookalike audiences from your best customers - keep CAC under control as you scale, it will try to climb protect the moat: 1: deepen community engagement 2: build integrations and partnerships that make leaving painful 3: create content flywheel that compounds (SEO, YouTube library, newsletter archive) metric to watch: brand search volume and organic vs paid ratio mistake to avoid: letting paid acquisition become your only growth channel -------- CONCLUSION most apps die between 100 and 1,000 users because founders skip retention and jump straight to ads the truth is: the first 3 stages are ugly, manual, and slow but they build the foundation that makes stages 4-7 feel like gravity start narrow. fix retention. then scale Growth is a system, make it effective ♥️ P.S. since this day, I will start showing what I build in public to show you how I grow revenue in my apps make the products and do an immediate ship for less than 1 week and how you can repeat this system.
Theo, after experiencing the superiority the TUI provided, was blown away. The fact that it worked flawlessly the first try, with speed and in perfect fashion, left him astonished, with no words. He took months to recover from this excellent experience, like he had just woken up from a bad dream, a dream where GUIs were superior to the terminal, but now that he was awakened, he saw the light. Right after, Theo became a core contributor of T1Code™, leaving the old and deprecated project T3Code™ behind. He figured that now everyone had seen the light on the better, more reliable, and quick experience TUIs offered, that no one will ever submit themselves to an inferior experience such as the GUI... and the world was never the same.
The Claw native app studio | Scale apps to $20k/mo with agents
Microsoft just dropped VibeVoice An open source voice AI stack that’s quietly pushing the limits of what speech models can do. Here’s why this is actually a big deal: → It can process 60 minutes of audio in a single pass No chunking. No broken context. No stitching errors. → It doesn’t just transcribe it understands structure You get: • Who spoke • When they spoke • What they said → Built-in speaker tracking + timestamps Basically ASR + diarization + formatting all in one model. → Supports 50+ languages natively Not an afterthought. Designed multilingual from the start. → You can guide it with custom hotwords Perfect for domain-heavy use cases (meetings, tech, healthcare, etc.) And that’s just the ASR side. There’s also: • Long-form TTS (up to 90 minutes, multi-speaker) • Real-time streaming voice (~300ms latency) • Lightweight deployment options (0.5B model) Under the hood, the interesting part: → Continuous speech tokenization at ultra-low frame rates → LLM + diffusion hybrid for better audio quality → Designed for long-context understanding (not just short clips) But here’s the part people shouldn’t ignore: High-quality voice generation = high risk of misuse. Deepfakes, impersonation, misinformation: all very real concerns. Even Microsoft explicitly warns against production use without safeguards. Still If you’re building in: • AI meeting assistants • Podcast tools • Voice agents • Transcription pipelines This repo is worth studying. Here's the GitHub: https://t.co/S1EpT40Ry0
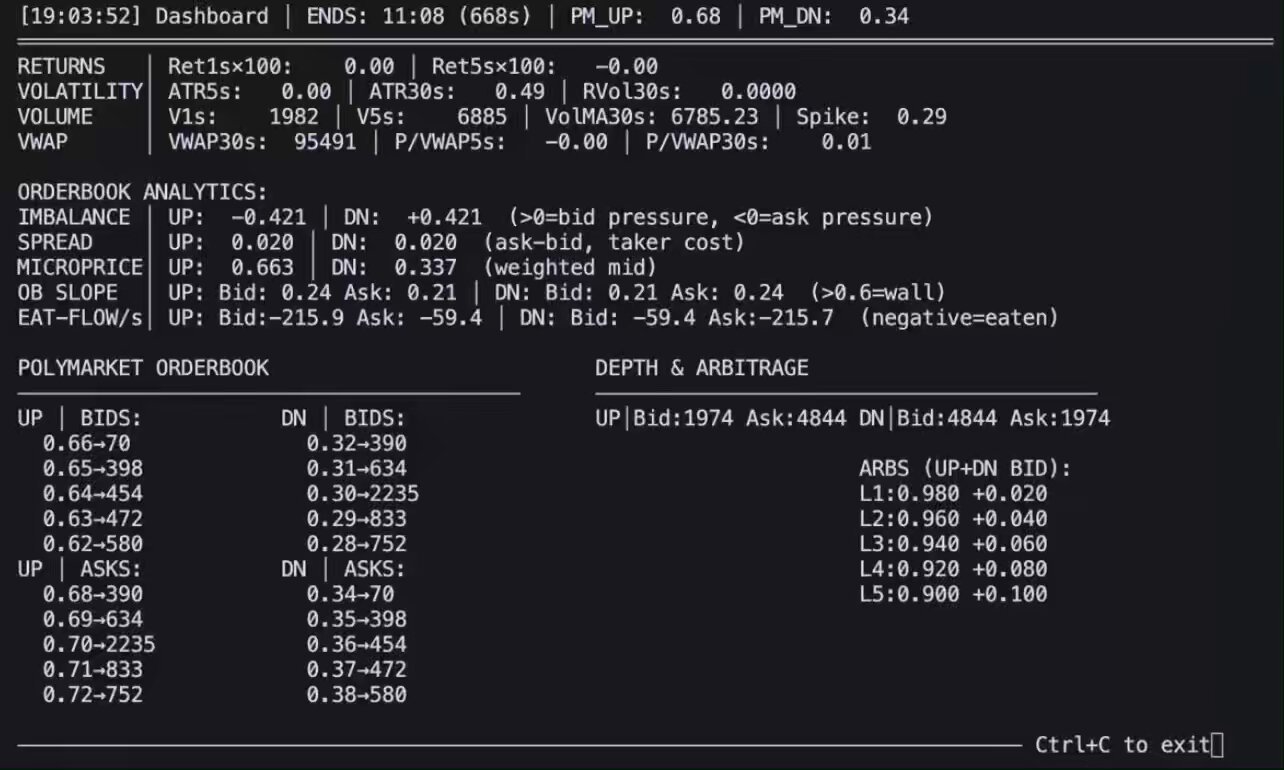
Alpha on Prediction Markets: Momentum, Value, Risk. The Complete Python Guide.
This model has been #1 trending for 3 weeks now. It's Qwen3.5-27B fine-tuned on distilled data from Claude-4.6-Opus (reasoning). Trained via Unsloth. Runs locally on 16GB in 4-bit or 32GB in 8-bit. Model: https://t.co/6KgPDHCJZ3
🚀 Qwen3.5-Omni is here! Scaling up to a native omni-modal AGI. Meet the next generation of Qwen, designed for native text, image, audio, and video understanding, with major advances in both intelligence and real-time interaction. A standout feature: 'Audio-Visual Vibe Coding'. Describe your vision to the camera, and Qwen3.5-Omni-Plus instantly builds a functional website or game for you. Offline Highlights: 🎬 Script-Level Captioning: Generate detailed video scripts with timestamps, scene cuts & speaker mapping. 🏆 SOTA Performance: Outperform Gemini-3.1 Pro in audio and matches its audio-visual understanding. 🧠 Massive Capacity: Natively handle up to 10h of audio or 400s of 720p video, trained on 100M+ hours of data. 🌍 Global Reach: Recognize 113 languages (speech) & speaks 36. Real-time Features: 🎙️ Fine-Grained Voice Control: Adjust emotion, pace, and volume in real-time. 🔍 Built-in Web Search & complex function calling. 👤 Voice Cloning: Customize your AI's voice from a short sample, with engineering rollout coming soon. 💬 Human-like Conversation: Smart turn-taking that understands real intent and ignores noise. The Qwen3.5-Omni family includes Plus, Flash, and Light variants. Try it out: Blog: https://t.co/yuSAz3DuO8 Realtime Interaction: click the VoiceChat/VideoChat button (bottom-right): https://t.co/nnAW9ZfRet HF-Demo: https://t.co/rLsqejKgCG HF-VoiceOnline-Demo: https://t.co/LIGtmITeSw API-Offline: https://t.co/lNE7fH5YUt API-Realtime: https://t.co/9A3lopXGwV
Breaking: Newly uncovered OpenAI Codex vuln enables command injection via GitHub branch names in task creation requests. Attackers could steal GitHub user access tokens & sensitive data. Full breakdown by Tyler Jespersen: https://t.co/7Q3TXVZSd1 #OpenAI #BTPhantomLabs https://t.co/DPAMfXS2KQ
🚀 Qwen3.5-Omni is here! Scaling up to a native omni-modal AGI. Meet the next generation of Qwen, designed for native text, image, audio, and video understanding, with major advances in both intelligence and real-time interaction. A standout feature: 'Audio-Visual Vibe Coding'. Describe your vision to the camera, and Qwen3.5-Omni-Plus instantly builds a functional website or game for you. Offline Highlights: 🎬 Script-Level Captioning: Generate detailed video scripts with timestamps, scene cuts & speaker mapping. 🏆 SOTA Performance: Outperform Gemini-3.1 Pro in audio and matches its audio-visual understanding. 🧠 Massive Capacity: Natively handle up to 10h of audio or 400s of 720p video, trained on 100M+ hours of data. 🌍 Global Reach: Recognize 113 languages (speech) & speaks 36. Real-time Features: 🎙️ Fine-Grained Voice Control: Adjust emotion, pace, and volume in real-time. 🔍 Built-in Web Search & complex function calling. 👤 Voice Cloning: Customize your AI's voice from a short sample, with engineering rollout coming soon. 💬 Human-like Conversation: Smart turn-taking that understands real intent and ignores noise. The Qwen3.5-Omni family includes Plus, Flash, and Light variants. Try it out: Blog: https://t.co/yuSAz3DuO8 Realtime Interaction: click the VoiceChat/VideoChat button (bottom-right): https://t.co/nnAW9ZfRet HF-Demo: https://t.co/rLsqejKgCG HF-VoiceOnline-Demo: https://t.co/LIGtmITeSw API-Offline: https://t.co/lNE7fH5YUt API-Realtime: https://t.co/9A3lopXGwV
How to finally trust Claude's advice (using Karpathy's LLM Council method)
Claude just tells you what you want to hear. Every time. You can’t trust it. So I built a skill that forces 5 AI advisors to argue about your question...
Computer use is now in Claude Code. Claude can open your apps, click through your UI, and test what it built, right from the CLI. Now in research preview on Pro and Max plans. https://t.co/s2FDQaDmr1
Introducing Codex Plugin for Claude Code
I built a new plugin! You can now trigger Codex from Claude Code! Use the Codex plugin for Claude Code to delegate tasks to Codex or have Codex review your changes using your ChatGPT subscription. Start by installing the plugin: https://t.co/u6gBpArwBc https://t.co/HyEdMPWees
https://t.co/Sbr574u8fu
I wanted to share a bunch of my favorite hidden and under-utilized features in Claude Code. I'll focus on the ones I use the most. Here goes.
Many are wondering "what Google saw" that caused them to revise their post-quantum cryptography transition deadline to 2029 last week. It was this: https://t.co/dQtmTK9pdz
🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.
🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.
🚨 CRITICAL: Active supply chain attack on axios -- one of npm's most depended-on packages. The latest axios@1.14.1 now pulls in plain-crypto-js@4.2.1, a package that did not exist before today. This is a live compromise. This is textbook supply chain installer malware. axios has 100M+ weekly downloads. Every npm install pulling the latest version is potentially compromised right now. Socket AI analysis confirms this is malware. plain-crypto-js is an obfuscated dropper/loader that: • Deobfuscates embedded payloads and operational strings at runtime • Dynamically loads fs, os, and execSync to evade static analysis • Executes decoded shell commands • Stages and copies payload files into OS temp and Windows ProgramData directories • Deletes and renames artifacts post-execution to destroy forensic evidence If you use axios, pin your version immediately and audit your lockfiles. Do not upgrade.
Many are wondering "what Google saw" that caused them to revise their post-quantum cryptography transition deadline to 2029 last week. It was this: https://t.co/dQtmTK9pdz
if you don't have these in your configs you're ngmi https://t.co/owzuqocAbk
Devin Review caught the axios supply chain attack for multiple Cognition customers before the attack was publicly known. These attacks will be 10x more frequent in the age of AI; it is critical that repo maintainers start using AI for defense as well. (showing one example below where Devin Review caught the attack within an hour of its release - text minorly edited for anonymization)
Claude code source code has been leaked via a map file in their npm registry! Code: https://t.co/jBiMoOzt8G https://t.co/rYo5hbvEj8
Claude code source code has been leaked via a map file in their npm registry! Code: https://t.co/jBiMoOzt8G https://t.co/rYo5hbvEj8
Claude code source code has been leaked via a map file in their npm registry! Code: https://t.co/jBiMoOzt8G https://t.co/rYo5hbvEj8
@Fried_rice i backed the source up on my github https://t.co/sAzTTn6NAr